When the power goes out at a manufacturing plant, it’s expensive. When it goes out at a defense facility, a military base, or a mission-critical government operation — it’s a security event.
The distinction matters more than most energy discussions acknowledge. For commercial and industrial facilities operating in sensitive sectors, grid outages don’t just disrupt production schedules or trigger equipment restarts. They can compromise surveillance systems, disable communication networks, interrupt classified operations, and create physical security vulnerabilities that take hours or days to fully assess.
And yet, despite this reality, many defense contractors, federal facilities, and mission-critical C&I operators are still approaching energy resilience the way everyone else does: a backup generator, a basic battery system on a static schedule, and a hope that the grid stays up.
That approach hasn’t aged well. Between aging grid infrastructure, more frequent extreme weather events, and a threat environment that increasingly targets energy systems as attack vectors, the tolerance for power disruption at critical facilities is effectively zero. Microgrid software is the layer that turns hardware assets into an intelligent, self-managing power system — and for this class of facility, the stakes are high enough that the software’s security architecture matters as much as its operational capabilities.
Key Insight: At defense and mission-critical facilities, a power outage isn’t an operational inconvenience — it’s a security event. The microgrid software managing your energy assets needs to be built with that reality in mind.

Why a Microgrid Is Only as Good as Its Software
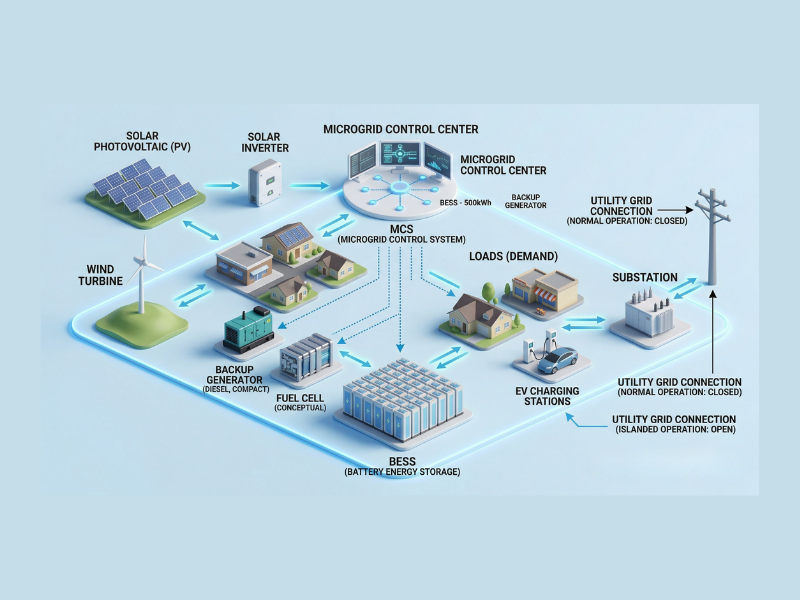
The hardware side of a microgrid is relatively well understood. Solar panels, battery energy storage systems (BESS), diesel or natural gas generators, and grid interconnection equipment all have established specs, performance benchmarks, and procurement pathways. Most facilities evaluating a microgrid have a reasonable sense of what they need on the equipment side.
What’s less appreciated is that the hardware is largely inert without an intelligent control layer. A battery sitting on a static charge/discharge schedule doesn’t respond to a sudden grid disturbance. A generator doesn’t know whether it should start because the grid has failed or because an automated system is simply testing it. Solar output doesn’t automatically compensate for a BESS that’s been depleted by an overnight demand spike.
Microgrid software — the energy management and control system that orchestrates all of these assets — is what makes the difference between a collection of expensive equipment and an actual resilient power system. It reads grid signals in real time, monitors asset health, makes dispatch decisions in milliseconds, and executes fault responses before a human operator could even identify the problem.
For a standard commercial facility, this is primarily a cost optimization question. For a defense or mission-critical operation, it’s an uptime and security question. And those two design objectives require different things from the software layer.
The Specific Capabilities Mission-Critical Facilities Need
Not all microgrid software platforms are built with the same operational priorities. Here is what defense contractors, federal facilities, and high-security C&I operators should be evaluating:
Automatic Islanding and Safe Mode: When the utility grid goes down, whether from a storm, infrastructure failure, or a targeted disruption, the microgrid needs to island itself from the grid and sustain facility power from local assets without human intervention. This transition needs to happen in seconds, not minutes. Any gap is a gap in security continuity. Look for platforms with automated safe mode functionality that immediately activates when grid anomalies are detected, protecting assets and maintaining operations without waiting for a manual command.
1+1 Redundancy: When it comes to critical infrastructure, there cannot be a single point of failure. The control architecture of the microgrid software itself needs to be redundant, meaning that if the primary control system encounters an issue, a secondary system can take over. This applies not just to hardware redundancy but to the software layer itself. Facilities should ask vendors directly: if your control platform goes offline, what happens to our energy assets? The answer should be ‘nothing changes’ — not ‘we work to restore service.’
Real-Time Anomaly Detection: The right microgrid software platform will continuously monitor battery state of charge, voltage levels, temperature, power quality parameters, including total harmonic distortion, and environmental conditions like humidity. When values drift outside normal operating ranges, automated alarms trigger and escalate through defined response protocols. For critical facilities, this anomaly detection isn’t just about asset longevity — it’s about catching the early signs of equipment failure before they cascade into an outage.
Escalating Incident Response: The best platforms have clearly defined escalation protocols. A low-severity notification goes to an operator; a high or critical alarm triggers an automatic escalation chain until a qualified person has acknowledged and responded. For facilities with 24/7 operations, the response chain needs to be automated and documented, not dependent on who happens to be watching a dashboard at 2 a.m.
Fire Alarm and Suppression Integration: BESS systems carry thermal risk. Any microgrid software operating in a facility with a battery installation should integrate directly with fire alarm and suppression systems, providing continuous monitoring and automated response. This is particularly important for defense applications where equipment densities are high and evacuation procedures are complex.
The difference between a microgrid that holds during a grid outage and one that fails is almost always in the control software — specifically, whether it was designed for passive monitoring or active, automated resilience.
Cybersecurity Is Not Optional — It’s Architecture
Energy systems at defense and mission-critical facilities are increasingly attractive targets for cyberattacks. The 2021 Colonial Pipeline incident demonstrated that energy infrastructure is a viable attack vector, and the sophistication of those attacks has only increased since. A microgrid software platform that isn’t built with enterprise-grade cybersecurity is a liability, regardless of how capable it is operationally.
The security architecture of the platform should be evaluated on several dimensions:
- Data Encryption: All data (both in storage and in transit) should be encrypted with AES-256, the same standard used for classified government communications. This is critical for any facility handling sensitive operations.
- Network Segregation: The microgrid control network should be isolated from the broader facility IT network using VLAN private networking. This limits the attack surface and prevents further damage if another part of the network is compromised.
- DDoS Protection: High-availability clusters with DDoS prevention ensure the control system remains operational even under deliberate attempts to overwhelm or disable it.
- Application-Level Segregation: Kubernetes-enhanced security provides isolation at the application layer, meaning that even if one software component is compromised, it cannot access other parts of the platform.
- Physical NOC Security: If the platform is managed by a Network Operations Center, that facility itself needs to meet physical security standards: biometric access controls, 24/7 surveillance, and an uninterruptible power supply. The irony of a microgrid management center going offline in a power event is not lost on facilities managers.
These aren’t features to negotiate on. They’re baseline requirements for any facility where a security breach through the energy management layer could compromise broader operations.
The Human Layer: 24/7 Monitoring Isn’t Just a Dashboard
One of the most common misconceptions about modern microgrid software is that a real-time dashboard is sufficient oversight. It isn’t — at least not for facilities where downtime has security consequences.
A dashboard tells you what’s happening right now. It doesn’t wake someone up at 3 a.m. when a battery cell temperature starts trending in a direction that suggests a problem in six hours. It doesn’t automatically dispatch a service call when a communication fault appears between the BESS management system and the control layer. And it doesn’t make the judgment call about whether a grid anomaly is a brownout that will self-correct or the beginning of an extended outage that requires islanding.
The facilities best positioned for energy resilience combine intelligent microgrid software with a dedicated Network Operations Center (NOC) staffed by specialists who understand both the technology and the operational context of what they’re protecting. Human judgment, backed by AI-driven anomaly detection and automated alerts, is the combination that actually delivers the uptime guarantees mission-critical facilities require.
For operations teams, this means not having to become BESS experts themselves. For C-suite leaders, it means the facility’s energy resilience is being managed with the same rigor as its cybersecurity or physical security programs — not delegated to whoever happens to be on shift.
The right question isn’t ‘do we have a microgrid?’ It’s ‘does our microgrid software know what to do faster than a human can respond — and is it built to handle the threat environment our facility actually faces?’
What This Means for C&I Facilities Beyond Defense
While the stakes are most visible in defense and federal contexts, the same operational logic applies to a broader class of commercial and industrial facilities: data centers, pharmaceutical manufacturers, water treatment facilities, hospital systems, and any operation where an unplanned outage carries consequences beyond lost revenue.
As grid reliability becomes less certain and energy markets become more complex, the divide between facilities with intelligent microgrid control and those without is going to become increasingly consequential. The ones with the right software layer will island seamlessly, maintain operations, and in some cases generate revenue by supporting the grid during stress events. The ones without will be waiting for the utility to restore power.
The hardware investment in solar, BESS, or backup generation is substantial. The software layer is what determines whether that investment actually delivers on its promise — or just sits there, waiting to be manually activated by someone who may or may not be available when it matters.
How NeuraCharge™ Addresses These Requirements
NeuraCharge™ by Edgecom Energy was built specifically for facilities that cannot afford to treat their energy storage and DER assets as passive infrastructure. It serves as the intelligent control layer for distributed energy resources — functioning, in effect, as the brain of your microgrid.
The platform provides real-time monitoring of battery performance parameters, environmental conditions, and power quality metrics, with automated alarms and a defined escalation structure for high and critical events. Automated safe mode activates during grid anomalies. 1+1 redundancy ensures control continuity if any single system component encounters an issue. The security architecture includes AES-256 encryption, VLAN network segregation, DDoS protection, and Kubernetes-enhanced application isolation.
For facilities requiring a higher level of managed service, NeuraCharge™ adds a dedicated Network Operations Center with 24/7 human-led surveillance, automated dispatch for energy programs, fire suppression system monitoring, and direct coordination with equipment manufacturers when service is required.
The platform is designed to sit above the battery management system and grid-level RTU, acting as the site-level control and monitoring layer without requiring replacement of existing equipment. Implementation is designed to be fast — reducing the engineering complexity and IT coordination that typically delays microgrid software deployments.
Ready to evaluate your facility’s microgrid resilience?
Speak with an Edgecom Energy engineer about how NeuraCharge™ can secure your energy assets and maintain operational continuity when the grid cannot.